
@HACK 2026
This year, I had the chance to participate in Canada’s largest student cybersecurity CTF: @HACK. This was my very first real-life CTF experience, and it was a lot of fun! I went with the DCI, my university’s cybersecurity/CTF club. There were two tracks available: the beginner and the regular track. My team competed in the beginner track and landed the 44th position out of 87 teams.
While we didn’t score very high, we had the chance of completing a very fun challenge, Alien Signals.
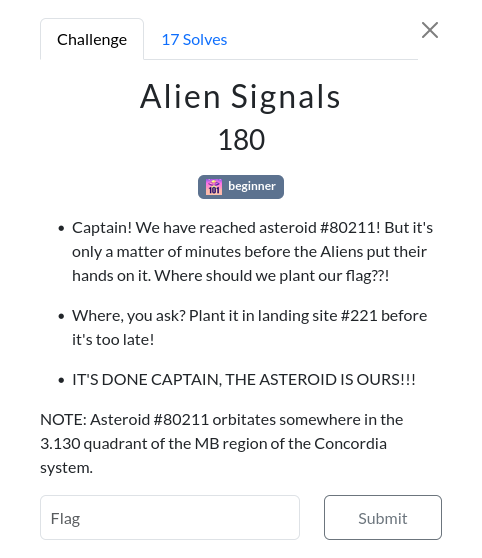
We found that the 3.130 quadrant of the MB region of the Concordia system was in reality a specific room in the MB building of Concordia University. My team and I went there, but didn’t find anything… until we understood that Asteroid #80211 was a reference to the 802.11 Wi-Fi standard.
We then scanned for nearby Wi-Fi SSIDs and there was the asteroid. Since it was password-protected, we didn’t really know what to do with it. Looking back at the challenge description, there was a mention of flag being planted in the landing site #221, which led us to think this might be a nearby room’s number. Since the challenge was in the Hardware category, we thought maybe we would find the router in this room. After a pretty long walk around two different floors of the building, we abandoned that idea…
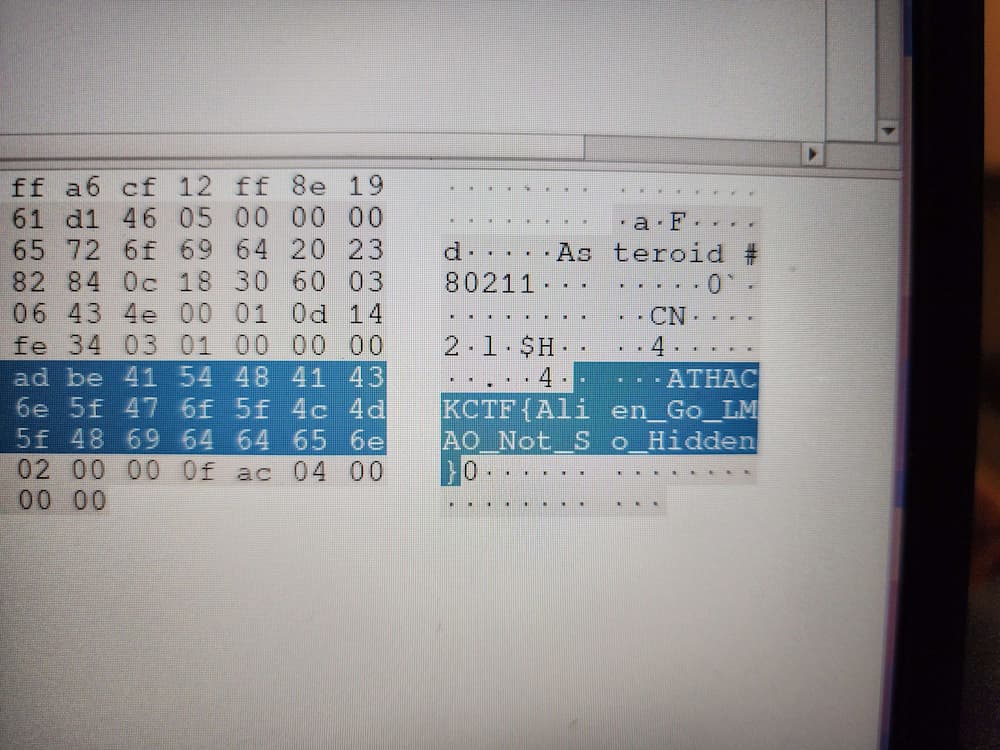
Researching further, we can find that, in the 802.11 standard, 221 could be a reference to the IE Vendor field. If the flag is planted in landing site #221, then we’ll probably find it there. By putting our laptop’s network card in monitor mode and capturing the packets with Wireshark, we analyzed the broadcast packet sent by the asteroid. After looking at the 221 field, we found the flag:
I am very thankful to have participated in this CTF, and am looking forward to the PolyPwn CTF later this month.